🎯 WEEKLY BRIEF
This week we introduce six new programs for you to start hacking, and getting PAID! 🤑
will be going over a brief introduction to John the Ripper!
How to install JTR
Single Crack attack
Brute force attack
Dictionary attack
Common hash types
🚀 TOP PROGRAMS TO HACK THIS WEEK
Here are six programs for you to start hacking this week!
🛠️ Cool Weekly Tool
John the Ripper
John the Ripper (JTR) is a widely used password auditing and security testing tool used by security professionals, sysadmins, and penetration testers to identify weak passwords in their own systems. 😎
We are going to be doing a very quick and brief intro to familiarize yourself with it.
View the basics of password cracking here
For this tutorial we will be using a Kali-Linux based environment. 🐉
Installation
Kali usually has John installed. Just check.
Ctrl Alt T to open terminal
john --versionIf not, simply update and install!
sudo apt update && sudo apt install johnHow Does It Work?
John works by taking a file of hashed passwords and attempting to recover the original plaintext using three main modes:
Single Crack: Uses login info with mangling rules.
Incremental : Brute force with character sets.
Wordlist: Tries passwords from a dictionary file.
Create test hash
echo -n "password" | md5sumExample output : 5f4dcc3b5aa765d61d8327deb882cf99 (copy)
save to a file:
vim hash.txt5f4dcc3b5aa765d61d8327deb882cf99 (paste)
Shift + ZZ to exit vim
Single Crack
This will use username info, and mangling rules automatically.
Since our file is just a hash with no username inside, it cannot use any username provided in the file.
But its worth trying 😉
john hash.txtLet John Loose. (Brute Force)
John shall automatically detect the hash type, and begin CRACKING!
john --incremental hash.txtNow this attack may take a while depending on your computers specs… so lets maybe try a dictionary attack instead?
A Dictionary Attack
A dictionary attack involves using.. well a list of words or common phrases. AKA a wordlist.
Kali will include rockyou.txt, but its compressed. So… UNZIP!
sudo gzip -d /usr/share/wordlists/rockyou.txt.gzRun That Dictionary Attack
We know the format is going to be MD5, so we will do that using —format=Raw-MD5 then again, john can figure this out on its own.
john --format=Raw-MD5 --wordlist=/usr/share/wordlists/rockyou.txt hash.txt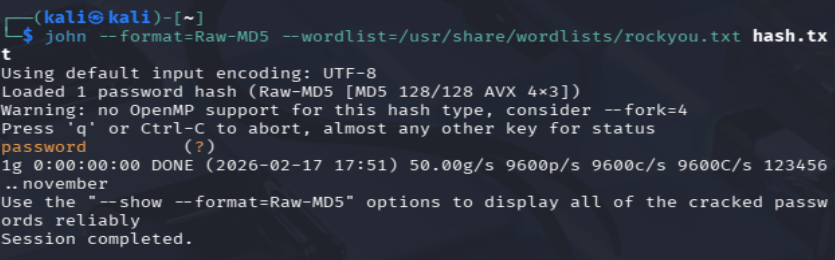
:0 see that “password (?)” that means john cracked the code!
See Password hash for the file that was cracked.
john --show --format=Raw-MD5 hash.txt
Common Hash Types + Flags
Hash Type | Format Flag |
|---|---|
MD5 |
|
SHA1 |
|
SHA256 |
|
bcrypt |
|